Visual Studio Code 1.112 brings agent permissions and integrated browser debugging improvements
Microsoft has released Visual Studio Code 1.112 with a heavy focus on tightening up security for agents and simplifying web app testing. This update gives developers more control over how Copilot CLI handles tasks without constant approval requests popping up in the terminal. Users will also find better tools for debugging modern web applications directly inside the editor window.
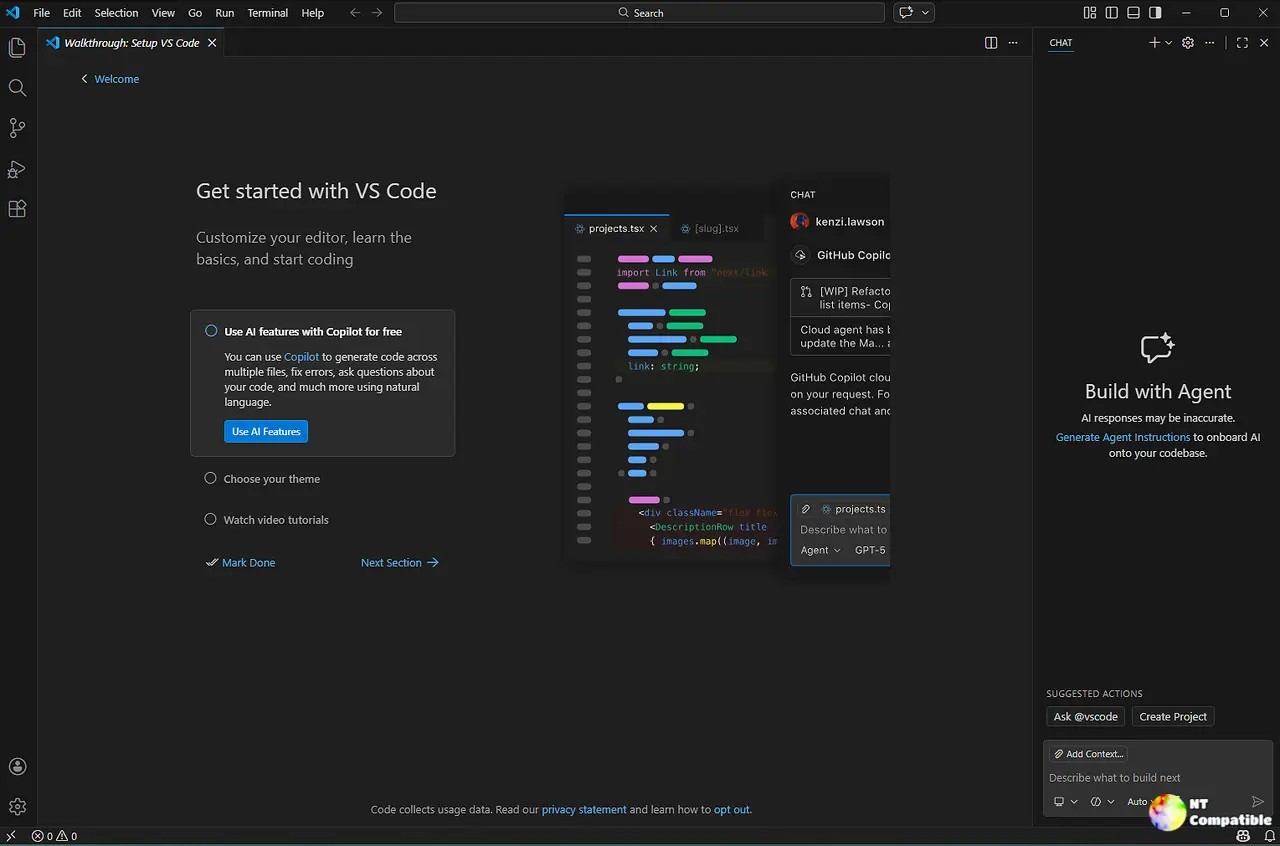
Visual Studio Code 1.112 agent permissions reduce interruptions
The biggest pain point with automated agents has always been asking permission to do every single file write or command run during a session. This release adds specific permission levels like Autopilot that allow the tool to work until a task is complete without constant confirmation dialogs blocking progress. A common scenario involves an agent trying to refactor code and getting blocked repeatedly on minor operations that slow down the entire workflow. With these new settings, the dynamic shifts from manual oversight to trusting the agent for defined scopes via the chat.autopilot.enabled configuration. Developers can now set high trust levels directly in the CLI to make automation feel less like a constant negotiation.
Integrated browser debugging works without leaving VS Code
Previously testing a web app meant switching between the code editor and an external browser window to inspect elements or run breakpoints effectively. Visual Studio Code 1.112 now supports debugging sessions directly within the integrated browser view for both Launch and Attach configurations. This means developers can set breakpoints in the source map and see variable states without alt-tabbing away from their workspace during complex troubleshooting. It is a practical change that saves time because context switching causes delays when trying to follow error traces across multiple windows. Most options from existing msedge and chrome debug configurations are supported which makes migration often as simple as changing the type of an existing configuration in launch.json.
MCP server sandboxing adds security for local tools
Running local Model Context Protocol servers used to grant them full access to the user's machine which posed unnecessary risks for sensitive data protection. The new sandboxing feature restricts file system and network access for these processes on macOS and Linux systems to limit potential damage from compromised plugins. This is a necessary safety measure because poorly written extensions can sometimes try to read sensitive configuration files or send data out over the network without user knowledge. Windows users will notice this does not apply yet but remote scenarios like WSL still function correctly as intended. To enable sandboxing one must set "sandboxEnabled": true for a server in their mcp.json file and allow VS Code to manage permissions interactively when access is required.
Troubleshooting commands help debug agent behavior
When an AI agent starts acting strangely it can be hard to know if a configuration file or a network issue is the culprit behind the slow response times. The new /troubleshoot skill analyzes debug logs directly in the conversation to provide insights into why tools were skipped or slowed down during execution. Enabling this requires turning on specific logging settings that export JSONL files to disk for detailed offline analysis later. It saves hours of guessing by showing exactly which instructions loaded and when errors occurred during the session using the github.copilot.chat.agentDebugLog.enabled setting.