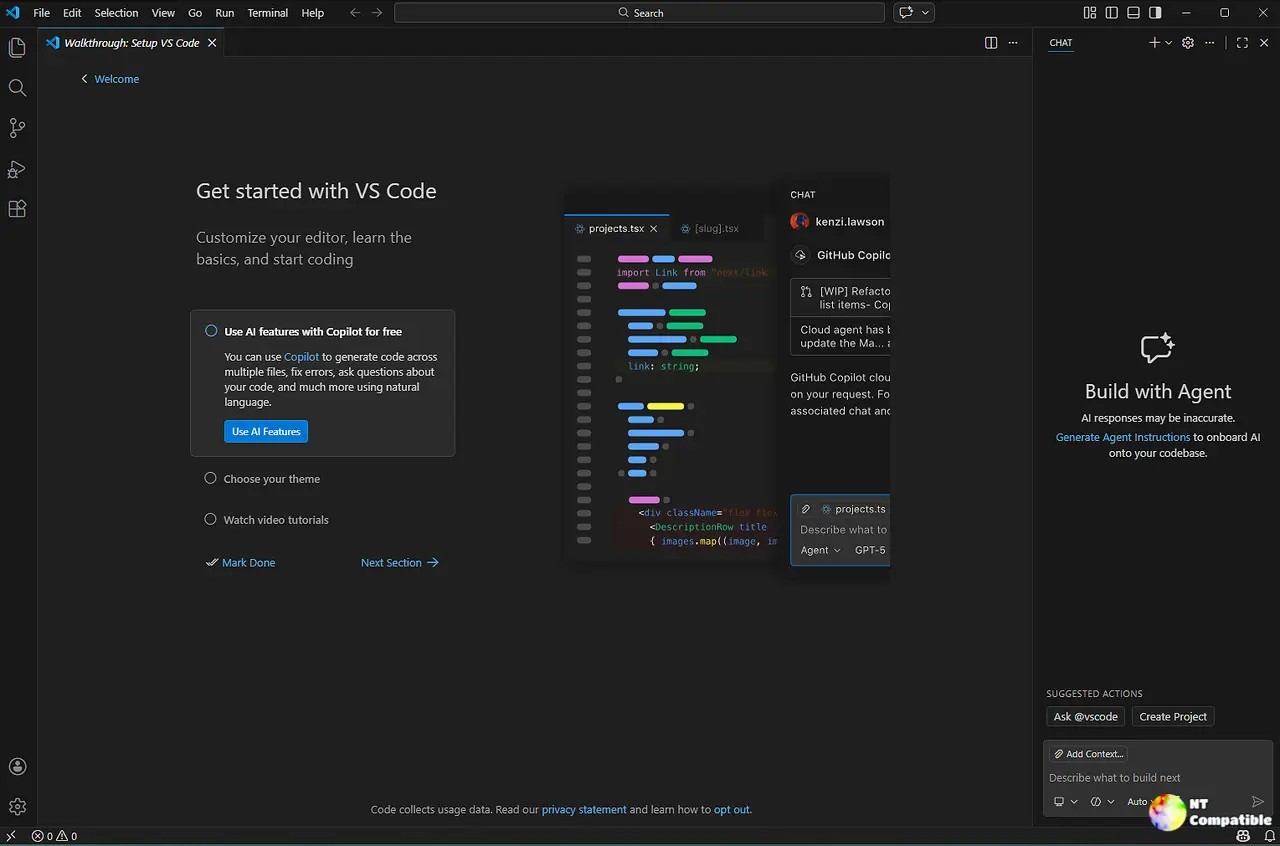
Visual Studio Code 1.119.1 Drops Critical Security Fixes You Need to Install
Visual Studio Code 1.119.1 just landed with a handful of security patches that directly address remote code execution risks and MCP integration flaws. Users who rely on untrusted workspaces or Jupyter notebooks should prioritize this update to keep their development environment from becoming a playground for exploit attempts. The release also wraps up the standard endgame cycle, meaning the next feature branch is already moving forward.
Security Fixes That Actually Matter
The update tackles two serious remote code execution vulnerabilities, one tied to webviews and another lurking inside Jupyter notebook markdown rendering. When the editor renders markdown in untrusted workspaces, it historically stripped out script execution, but edge cases in the rendering pipeline occasionally let malicious payloads slip through. Developers have seen this exact pattern repeat after a routine dependency update or when someone shares a seemingly harmless notebook file. Microsoft patched the markdown renderer to enforce stricter sandboxing rules, which is exactly what should happen when handling untrusted content. Allowing raw script execution in a rendered preview is just asking for trouble. The webview fix closes a similar escape route that could allow arbitrary code execution under the right conditions. These kinds of vulnerabilities tend to show up when the extension host tries to read workspace settings without proper isolation checks.
How the MCP and Sensitive File Patches Change Things
Visual Studio Code 1.119.1 also addresses a messy MCP deeplink installation issue that left essential configuration data out of the process. When users clicked through a server link, the client sometimes failed to register the correct authentication tokens or workspace scope. That meant the chat tool would silently drop requests or fall back to default behavior, which is a frustrating waste of time. The patch ensures the deeplink handler passes all necessary parameters during registration. Alongside that, the release applies a workaround for a sensitive file handling bug that previously allowed certain configuration paths to leak into chat contexts. This kind of data bleed usually happens when the extension host tries to read workspace settings without proper isolation checks. The fix tightens the boundary between chat tools and raw file access, which keeps accidental credential exposure from becoming a routine annoyance.
Installing the Update Without Breaking Existing Configurations
Download the latest installer from the official site and run it over the existing directory. This approach preserves user settings and extensions by default, so switching over rarely causes configuration drift. Anyone who uses custom shell profiles or third-party terminal integrations should run a quick test after installing to confirm that workspace trust prompts still appear correctly. Verifying the installation prevents broken extension hosts from silently eating up system resources. The standard update prompt will push the new build to the stable channel, while insiders using the Insiders build will see the changes immediately. Users who manage corporate environments or use portable installations should grab the latest installer manually to avoid automatic channel switches that might interfere with group policy restrictions.
What Comes Next in the Release Cycle
The endgame plan for this build is already closed, which means the team has moved on to stabilizing the next feature set. Development workflows typically freeze security patches in the current version while the next branch picks up new APIs and interface changes. Users who prefer a steady environment should stay on the stable channel until the next minor version hits the same quality bar. Those who want early access to chat improvements and workspace management tweaks can switch to the Insiders build without affecting their primary installation. The codebase continues to separate MCP handling from core rendering logic, which should reduce the kind of cross-component bugs that showed up here.
Release VSCode 1.119.1 · microsoft/vscode
The update addresses these issues https://code.visualstudio.com/updates/v1_119
Keep the terminal open and the updates current. Happy coding.